Errr ok, so the “NSA-style content searching” might be a bit overrated then again it’s usually only the intelligence agencies which perform this type of bulk searches as far as I know. Anyhow, here is an idea on how to abuse Google DLP (available in google apps for work) to perform exactly the same, since it recently incorporated support to also perform OCR on the emails / attachments:
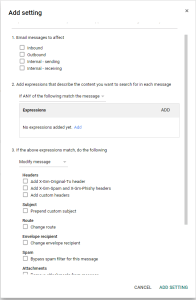
According to this screenshot it seems that you can also perform DLP actions on incoming items:
Which is what enables us to perform specific content searches on all incoming email messages and prepend certain keywords to the subject. Now imagine you just hacked an organisation and added a rule to the exchange server or individual outlook instances to forward all email to an email your control and has DLP enabled with all the keywords, hashes or rules you need to only get the juicy contents out? Don’t forget to delete the forwarded message with a rule ;) The types of content matching that you can perform is also pretty flexible:
- Pattern match—A specific alphanumeric pattern (not just string length), including delimiters, valid position, and valid range checks
- Context—Presence of relevant strings in proximity to pattern and/or checksum matching string
- Checksum—Checksum computation and verification with check digit
- Word/phrase list—Full or partial match to an entry found in a dictionary of words and phrases
Based on the DLP trigger you can then just rename the subject and use google rules to forward the message to another inbox or leave it there and just organise it into folders. Kinda saves you as an attacker a lot of time, since normally you’d have to perform or implement OCR / content matching yourself. Added bonus is that since it’s already been stolen from the victim company it doesn’t really matter what you do with it as long as the original sender doesn’t receive some weird Google notification.
You might be thinking “my client will never allow this”, but what if your client is already connected to google apps for work?
As a final thought you could also use this for defence purposes if you are already working with Google apps for work as an organisation. You could use the Google DLP feature to feed it the currently hyped ‘threat intelligence’ file hash information and block different known threat actors if their tools & techniques remain the same for a period of time.