Apparantly sometimes you only grasp it when it really is in your face, even though you are continuously surrounded by it. The following tweet, made me realize that real consequences to vulnerabilities matter a lot! Oh and this blog is mostly some ponderings and opinions, for the people wondering if they should read it or not :)
What this tweet made me realize is that for Lockbit the consequence of the bug is directly tied to their income. No indirect damages, no additional bugs, no excuses. If the bug isn’t fixed people don’t need to pay them. How many type of companies and bugs do we know that have the same 1-to-1 relation between the bug and the direct consequence to survival?
This made me wonder if we are approaching the rating & fixing of vulnerabilities within regular companies in a less than optimal manner? Would be interesting if we could learn something from groups that operate on continuous innovation and the severe threat of real life consequences like jail time or worse. In this blog I’ll talk about:
- Analysing the Lockbit bug bounty
- Applying the lessons learned to regular companies
TL;DR Bloodhound showed us that graphs are powerful for the analysis and elimination towards domain admin privileges. The same concept should be applied to vulnerablities company wide. Regular companies don’t have the same severe consequences that ransomware groups have, should they?
Analysis
The only type of companies that come to mind are gaming companies. Any vulnerability in their DRM system (for the ones that choose to implement this measure) results in less games sold (let’s not dive into buying motivations and the ethics of DRM). As is the case with ransomware it also scales. What I mean is that a bug in the encryption algorithm of the ransomware group scales to all victims, thus it also scales to monetary loss. Sames goes for a bug in DRM, it scales to all games sold / in posession of buyers.
Regular companies need to fix vulnerabilities & make money, which as we would all expect means they usually don’t invest in security as they should, since the risks are considered manageable. We witness that every day with the ransomware attacks or espionage attacks etc. Could that potentially be, due to the fact that the vulnerabilities don’t have a direct correlation to their survival?
Just to be sure, let look at the bug bounty program from Lockbit to understand how many of their bounties are directly tied to their survival:
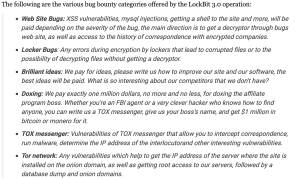
source: https://www.bleepingcomputer.com/news/security/lockbit-30-introduces-the-first-ransomware-bug-bounty-program/
Let’s analyse the Lockbit bug bounty clauses to understand how many of them have a direct consequence:
- Web site bugs – Partial, they hint strongly on obtaining the decryptor type of bugs and the correspondance with compnies. Of these two, only the decryptor has a strong impact on their survival
- Locker bugs – Direct, it impacts their ability to receive money if people can recover their files for free
- Brilliant ideas- None, doesn’t classify as vulnerability
- Doxing – Direct, besides the threat of jail time, like any company it could be very difficult times ahead
- Tox messenger – Partial – although it helps the investigation into them a lot, they don’t suffer direct damages to their operation. It could take a while before this materializes into consequences they have to deal with
- Tor network – Partial – although it helps the investigation into them a lot, you can read in their text that just getting their IP isn’t sufficient. You’d need additional bugs to for example dump their database which might contain decryption keys.
So that leaves us with a total of 5 types of clauses that are eligibale for the analysis. Out of these 5 clauses that we analyzed: 2 direct consequences and 3 partial consequences. Let’s recap the consequences as well to understand the actual consequences of the vulnerabilities:
- Jail time – well kind of obvious not a lot of people want to voluntarily sit in jail
- Loss of income – if you can decrypt without paying, they don’t make money
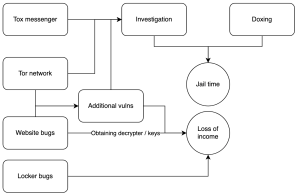
By visualizing it into a graph we can measure two things:
- Which vulnerabilities impact multiple chains / paths?
- Which vulnerabilities are directly connected to the consequence?
Application to regular companies
Sooo, what does all of this exactly mean or how does this translate to regular companies? To be honest, I think regular companies just don’t have that strong of a consequence to fix vulnerabilities or issues. The only consequence I can think of is the GDPR one, which directly impacts their income in the form of a fine. And even so, for some companies that is still peanuts. Would be interesting if the size of the GDPR fine would scale in relation to the amount of data obtained.
If we stick with the graph visualization of the link between vulnerability and consequence I’d say that we need to better understand which chain of vulnerabilities leads to a consequence that really has impact. Then prioritize the fixing of bugs based on the amount of chains that they disrupt or their distance to the real consequence.
Publishing real consequences and the corresponding chains could in addition help a lot of companies to better undertand risk and the value of different vulnerabilities in different contexts. For example:
DDOS would be addressed much quicker by a company that directly depends on availability as the source of income, than a company that doesn’t depend on it.
Domain admin is for almost nobody a direct consequence, it is only one link within the chain, same goes for obtaining domain admin. That usually consists of multiple links that form their own chain (for which we have the lovely bloodhound to mostly solve this issue)
Ransomware is for almost nobody a direct consequence. As far as I’ve seen the real consequence is in specific information or systems being ransomed. Most companies also seem to survive the attacks and keep doing business (even at a great financial cost). Ransomware itself consists of multiple chains with multiple vulnerability links. Which one of those links disrupts the most chains or has a direct impact on a critical system?
So, to conclude my pondering at 00:12 in the evening. I think that if we want to learn from ransomware groups how to deal with vulnerabilities, we should really think in terms of chains & direct connections with real consequences for companies. Although I remain sceptical in identifying consequences that are as direct & severe as the ones that ransomware groups face.
One thought on “Lockbit’s bounty: consequences matter”