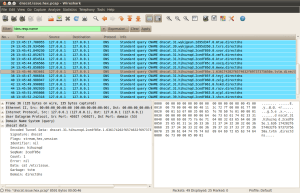
Well previously I blogged about actually parsing DnsCat traffic, this blog post will be about converting it into an actual Wireshark post-dissector. As with dissecting DnsCat traffic using LUA I’ve also never written a wireshark post-dissector up until now. This is how it will finally look like:
Things you should know(read: things that could/should be improved) about this post-dissector:
- It assumes you are tunneling plain ascii (dnscat –listen –exec ‘/bin/sh’)
- It will only decode incoming&outgoing packets if you use the wireshark development version
- I think it would be more efficient if this would have been a chained-dissector
- It’s only been tested locally (dnscat –dns 127.0.0.1)
- It will happily parse every DNS packet it encounters
Just as the previous post, this one will contain the source code (pastebin) and the references at the end of the post. Now let’s get going with building our post-dissector.